
APA Style
Idris Olanrewaju Ibraheem, Abdulrauf Uthman Tosho. (2025). A Unified Snort–OSSEC Hybrid Intrusion Detection Framework for Cloud Security. Communications & Networks Connect, 2 (Article ID: 0010). https://doi.org/Registering DOIMLA Style
Idris Olanrewaju Ibraheem, Abdulrauf Uthman Tosho. "A Unified Snort–OSSEC Hybrid Intrusion Detection Framework for Cloud Security". Communications & Networks Connect, vol. 2, 2025, Article ID: 0010, https://doi.org/Registering DOI.Chicago Style
Idris Olanrewaju Ibraheem, Abdulrauf Uthman Tosho. 2025. "A Unified Snort–OSSEC Hybrid Intrusion Detection Framework for Cloud Security." Communications & Networks Connect 2 (2025): 0010. https://doi.org/Registering DOI.
 ACCESS
Research Article
ACCESS
Research Article
Volume 2, Article ID: 2025.0010

Idris Olanrewaju Ibraheem
ioibraheem@alhikmah.edu.ng

Abdulrauf Uthman Tosho
autosho@alhikmah.edu.ng
Department of Computer Science Faculty of Computing, Engineering and Technology Al-Hikmah University, Adewole Estate, Ilorin, Nigeria
* Author to whom correspondence should be addressed
Received: 03 Aug 2025 Accepted: 15 Nov 2025 Available Online: 16 Nov 2025
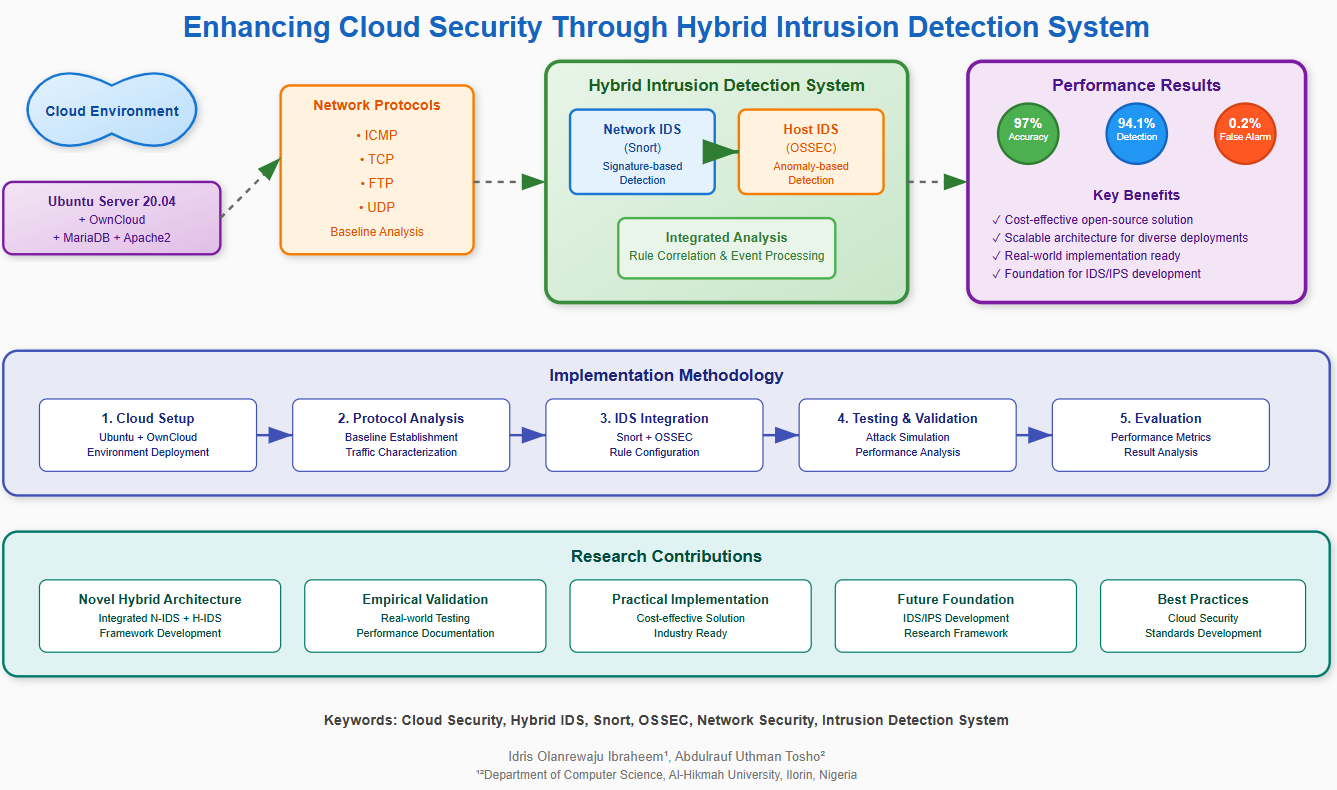
The growing adoption of Cloud computing has brought about the enhancement of cost-efficiency and effectiveness but also comes with increase in security vulnerabilities due to its distributed and multi-tenant architecture. This contribution if this study to the cloud security through the development of a hybrid intrusion detection system (IDS) that integrates Snort (N-IDS) and OSSEC (H-IDS) to achieve cross-layer alert correlation. Unlike standalone deployments or other deep learning models that are computationally intensive, the framework proposed is an open source that is interpretable, and also deployable in real-world environments. The experimental evaluation within a cloud testbed shows that the hybrid IDS was able to achieve 97.1% accuracy, a 94.1% detection rate, and a false alarm rate of only 0.2%, which performed better than Snort-only and OSSEC-only systems. The case-based simulations conducted further revealed that hybrid correlation does not just enhance the detection, but it also reduced false positives with better forensic trails, most especially in port scanning, brute-force login, and user-to-root exploits. When compared with previous IDS studies, the system achieved competitive accuracy while maintaining efficiency and transparency. Although tested in a limited-scale environment, this study establishes a practical foundation for adaptive, scalable, and prevention-oriented frameworks in cloud security.
Disclaimer: This is not the final version of the article. Changes may occur when the manuscript is published in its final format.
We use cookies to improve your experience on our site. By continuing to use our site, you accept our use of cookies. Learn more