
APA Style
Yih-Chang Chen, Chia-Ching Lin. (2025). The Application of IoT Technology in Social Work: Innovative Models for Home Care of the Elderly. Computing&AI Connect, 2 (Article ID: 0025). https://doi.org/Registering DOIMLA Style
Yih-Chang Chen, Chia-Ching Lin. "The Application of IoT Technology in Social Work: Innovative Models for Home Care of the Elderly". Computing&AI Connect, vol. 2, 2025, Article ID: 0025, https://doi.org/Registering DOI.Chicago Style
Yih-Chang Chen, Chia-Ching Lin. 2025. "The Application of IoT Technology in Social Work: Innovative Models for Home Care of the Elderly." Computing&AI Connect 2 (2025): 0025. https://doi.org/Registering DOI.
 ACCESS
Research Article
ACCESS
Research Article
Volume 2, Article ID: 2025.0025

Yih-Chang Chen
cheny@mail.cjcu.edu.tw

Chia-Ching Lin
lincc@mail.cjcu.edu.tw
1 Department of Information Management, Chang Jung Christian University, Tainan 711, Taiwan
2 Bachelor Degree Program of Medical Sociology and Health Care, Chang Jung Christian University, Tainan 711, Taiwan
3 Department of Finance, Chang Jung Christian University, Tainan 711, Taiwan
* Author to whom correspondence should be addressed
Received: 12 Jun 2025 Accepted: 30 Sep 2025 Available Online: 01 Oct 2025
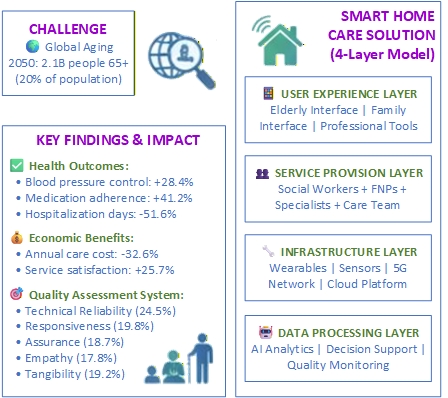
This research investigates the transformative influence of Internet of Things (IoT) technology on home care services for the elderly within the domain of social work. In light of the accelerating global trend of population aging, it is anticipated that by the year 2050, the number of individuals aged 65 and older will reach 2.1 billion, representing approximately 20% of the total global population. Traditional institutional care models encounter significant challenges, including high costs and a lack of personalized care. This study employs a mixed-methods approach, incorporating literature review, expert consultation via the Delphi method, and the analytic hierarchy process to develop a quality assessment indicator system for smart home care services. The findings indicate that IoT technology, through its capabilities of sensing, predicting, reminding, and responding, can effectively monitor the daily living conditions of elderly individuals and provide timely support, thereby significantly reducing hospitalization rates and improving overall quality of life. Family Nurse Practitioners (FNPs) are identified as pivotal figures in this innovative model, with an expanded scope of practice that encompasses personalized health assessments, disease diagnosis, medication prescriptions, and chronic disease management. This study advocates for an integrated smart home care model, offering novel solutions to the challenges posed by an aging population.
Disclaimer: This is not the final version of the article. Changes may occur when the manuscript is published in its final format.
We use cookies to improve your experience on our site. By continuing to use our site, you accept our use of cookies. Learn more