APA Style
Mircea Ţălu. (2026). Temporal DNA-Based Key Derivation and Metadata Fingerprinting for Secure On-Device Digital Forensics in IoT Systems. Computing&AI Connect, 3 (Article ID: 0032). https://doi.org/Registering DOIMLA Style
Mircea Ţălu. "Temporal DNA-Based Key Derivation and Metadata Fingerprinting for Secure On-Device Digital Forensics in IoT Systems". Computing&AI Connect, vol. 3, 2026, Article ID: 0032, https://doi.org/Registering DOI.Chicago Style
Mircea Ţălu. 2026. "Temporal DNA-Based Key Derivation and Metadata Fingerprinting for Secure On-Device Digital Forensics in IoT Systems." Computing&AI Connect 3 (2026): 0032. https://doi.org/Registering DOI.
 ACCESS
Research Article
ACCESS
Research Article
Volume 3, Article ID: 2026.0032
Mircea Ţălu
talu.s.mircea@gmail.com
1 Department of Computer Science, Faculty of Automation and Computer Science, The Technical University of Cluj-Napoca, 26-28 George Barițiu St., Cluj-Napoca, 400027 Cluj, Romania
2 SC ACCESA IT SYSTEMS SRL, Constanța St., no. 12, Platinia, CP. 400158 Cluj-Napoca, Romania
Received: 23 Sep 2025 Accepted: 16 Mar 2026 Available Online: 17 Mar 2026
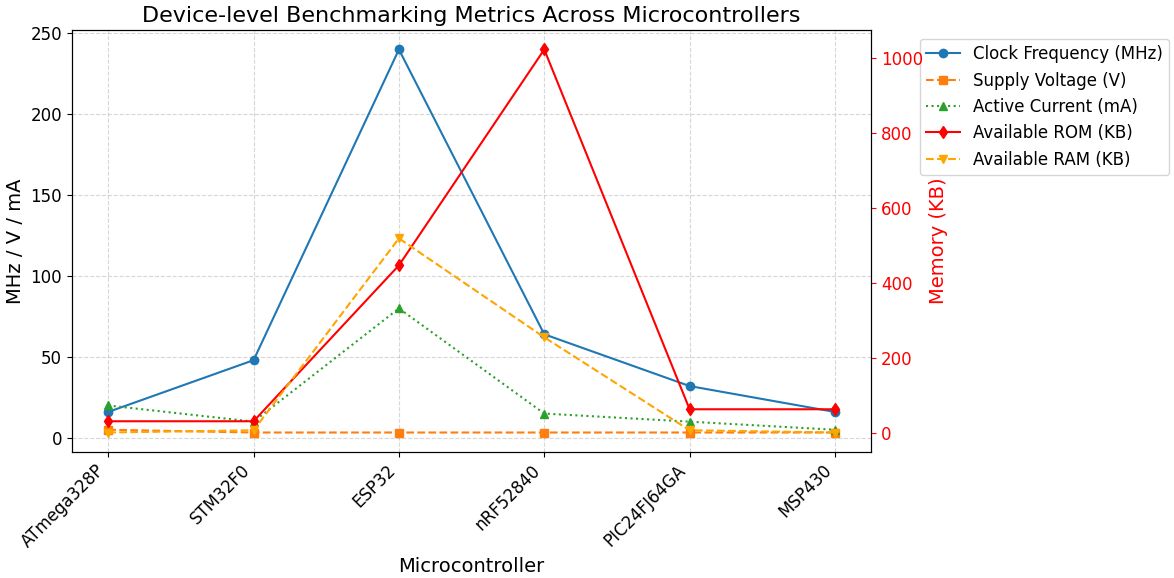
This study benchmarks a temporal DNA-based key derivation function (DNA-KDF), against eleven lightweight block ciphers (PRESENT-80, ASCON-128, SPECK-64, TWINE-80, HIGHT, SIMON-64/128, LED-64, QARMA, LEA, SEPAR, and BORON) on six representative IoT microcontrollers (ATmega328P, STM32F0, ESP32, nRF52840, PIC24FJ64GA, MSP430). Performance evaluation covers execution latency, memory footprint, throughput, energy consumption, and security metrics. Results show that SPECK-64 and SIMON-64/128 achieve the lowest latency (0.72–2.08 ms) and highest throughput (up to 1200 kB/s), confirming their efficiency in constrained devices. DNA-KDF demonstrates moderate latency (1.03–2.47 ms) and throughput up to 1000 kB/s, outperforming ciphers such as TWINE-80, HIGHT, and BORON on several platforms. Its memory demand (2.50 KB ROM / 0.32 KB RAM) is higher than classical designs but remains feasible for modern IoT nodes. The energy measurements show that DNA-KDF consumes between 3.2 and 6.9 μJ, which falls within an acceptable range. Its energy use is similar to HIGHT and lower than that of PRESENT-80 and SIMON-64/128. The security tests demonstrate good performance, with an avalanche effect close to the ideal value (49.8%), high entropy values (7.98–7.99 bits per byte), and strong sensitivity to key changes. These results indicate that DNA-KDF provides a level of security comparable to ASCON-128. When compared with AES-128, DNA-KDF runs about 50% faster and requires approximately 25% less energy. The findings suggest that DNA-KDF is a practical and effective additional security solution for mid-level IoT devices, offering a good balance between new design concepts and real-world efficiency.
Disclaimer: This is not the final version of the article. Changes may occur when the manuscript is published in its final format.
We use cookies to improve your experience on our site. By continuing to use our site, you accept our use of cookies. Learn more